-
JupyterHub
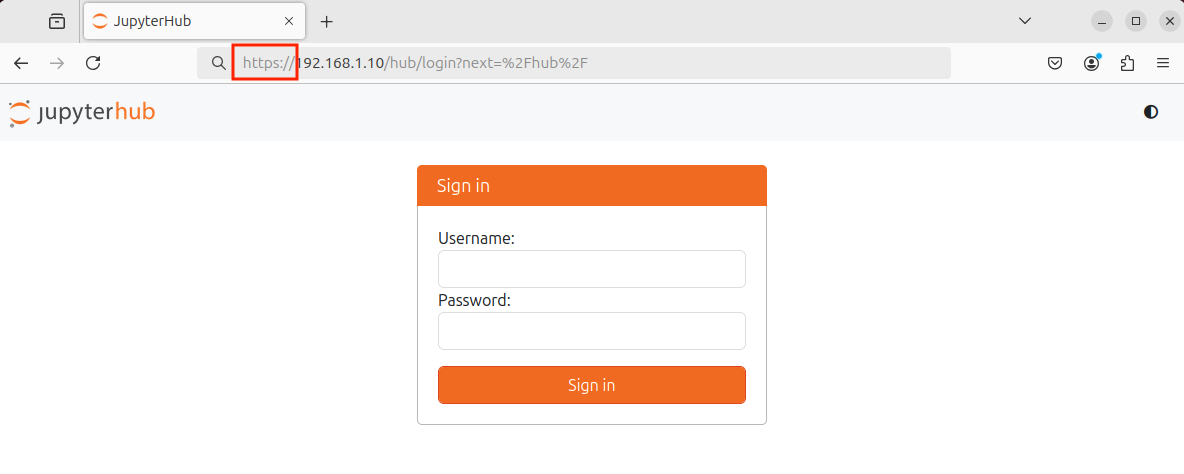
JupyterHub JupyterHub is an open-source platform that provides multi-user access to Jupyter Notebook or JupyterLab environments. While JupyterLab or the single-user Jupyter Notebook server is suitable for individual users, JupyterHub is ideal for educational institutions, research groups, or organizations that need multiple users to have their own interactive computing environments on a shared server. Each…
-
JupyterLab
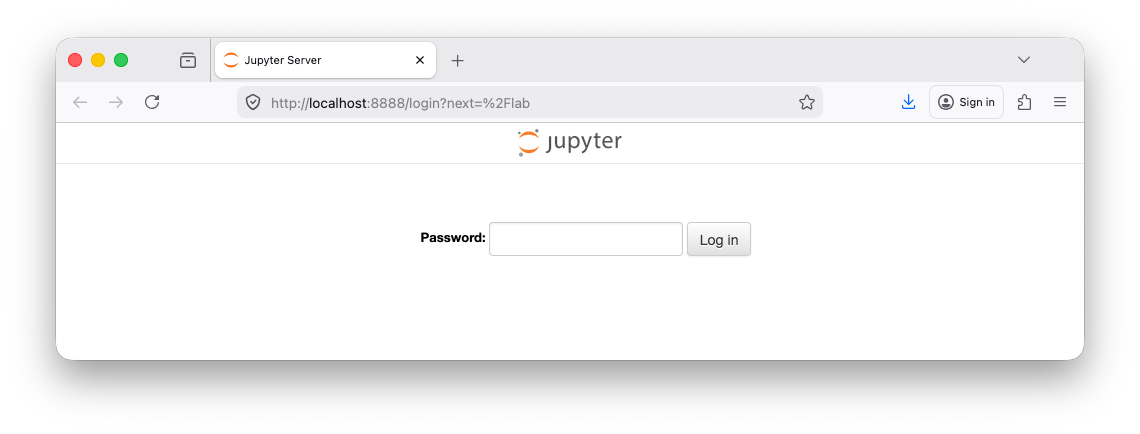
JupyterLab JupyterLab is an open-source web-based interactive development environment primarily used for data science, scientific computing, and machine learning. It allows users to create and manage interactive documents that combine live code, visualizations, equations, and narrative text in a single workspace. These documents are saved with the .ipynb extension, which stands for IPython Notebook, reflecting…
-
Electrical Energy and Circuits
Electricity Electricity is the flow of electrons through a conductor (like wires). It powers lights, devices, and machines. Alternating Current (AC) Alternating Current (AC) is electricity that reverses direction as it flows, moving back and forth instead of in one direction. This change happens rapidly and repeatedly in a wave-like pattern. AC is commonly used…
-
Web Servers
Webserver A software application that delivers web content, such as HTML pages, images, videos, and other resources, to end users over the internet or a network. When a user requests a web page in a browser, the web server processes the request, retrieves the requested content, and sends it back to the client using HTTP…
-
Honeypots
Honeypot A decoy application or system, commonly known as a honeypot, is a carefully designed and intentionally vulnerable tool used as bait to attract and trap cyber attackers. By simulating real systems, services, or applications, honeypots create realistic targets that appear valuable to threat actors. This approach enables organizations to observe attacker behavior, study tactics,…
-
Message Queuing Telemetry Transport Protocol
Network Protocol A network protocol is a standardized set of rules procedures and conventions that govern how data is formatted transmitted and received between devices on a network These protocols ensure that devices regardless of their manufacturer operating system or hardware can communicate reliably and efficiently enabling the seamless exchange of information across networks. Network…
-
IT, OT, IoT, and IIoT Networks
Computer Network A computer network is a system of interconnected devices such as computers, servers, routers, and other hardware that communicate to share data, resources, and services. Networks create pathways and infrastructure for the flow of information between devices, enabling activities such as sending emails, browsing the web, streaming video, or participating in video calls.…
-
Operating System Filesystem
Windows File System The Windows File System is basically how Windows organizes, stores, and manages all the data on a computer’s drives. Linux-Based OS File System The Linux-based OS File System is how Linux-based OS organizes, stores, and manages all the data on a computer’s drives. Windows vs Linux-Based OS
-
Microcomputer Operating System Forensics
Online (Live) Digital Forensics Online digital forensics is conducted while the system is running and may be connected to a network. This approach captures volatile data, such as RAM contents, running processes, network connections, open files, and active sessions, information that would be lost if the system were shut down. This method is particularly useful…
-
Hardening Microcomputer Operating Systems
IoT Security IoT Security involves safeguarding Internet of Things (IoT) devices and the networks they connect to from unauthorized access, misuse, data breaches, and other cyber threats. IoT devices frequently operate with limited computing power, minimal built-in security, and are deployed in large numbers, making them attractive targets for attackers seeking to exploit vulnerabilities. A…