Webserver
A software application that delivers web content, such as HTML pages, images, videos, and other resources, to end users over the internet or a network. When a user requests a web page in a browser, the web server processes the request, retrieves the requested content, and sends it back to the client using HTTP or HTTPS. Two of the most common web servers are Apache and Nginx. Apache uses a thread-based approach, creating a separate thread for each incoming request, which allows it to handle requests individually and can make it faster in some scenarios, especially when processing dynamic content. Nginx, on the other hand, uses an event-driven, asynchronous architecture that efficiently handles a large number of simultaneous connections, making it highly suitable for serving static content and acting as a reverse proxy or load balancer.
Apache Web Server
You can download an Apache web server using the apt-get command
sudo # Run the command with superuser (administrator) privileges
apt-get # Linux package management command used to handle software packages
update # Option to refresh the local package index with the latest versions available from repositories
(RPi) sudo apt-get updatesudo # Run the command with superuser (administrator) privileges
apt-get # Linux package management command used to handle software packages
install # Option to install a specified package
apache2 # Specify that you want to install the apache2 package
(RPi) sudo apt-get install apache2After installing it, you need to start it, Apache runs in the background, so you will need to start the Apache service using the systemctl command
sudo # Run the command with superuser privileges
systemctl # Command to control systemd services
start # Option to start the specified service immediately
apache2 # The apache2 service to be started
(RPi) sudo systemctl start apache2Web servers serve web content on port 80. To check if apache2 is listening on port 80, you can use the netstat command
sudo # Run the following command with superuser (root) privileges
netstat # Network statistics tool that shows network connections, routing tables, interface stats, etc.
-t # Show TCP connections only
-u # Show UDP connections only
-p # Show the PID and name of the program using each socket
-l # Show only listening sockets (services waiting for connections)
-a # Show all sockets (both listening and non-listening)
-n # Show numerical addresses instead of resolving hostnames
(RPi) sudo netstat -tuplan
Active Internet connections (servers and established)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 548/sshd: /usr/sbin
tcp6 0 0 :::80 :::* LISTEN 4524/apache2
tcp6 0 0 :::22 :::* LISTEN 548/sshd: /usr/sbin
udp 0 0 0.0.0.0:68 0.0.0.0:* 536/dhcpcd
udp 0 0 0.0.0.0:5353 0.0.0.0:* 386/avahi-daemon: r
udp 0 0 0.0.0.0:42997 0.0.0.0:* 386/avahi-daemon: r
udp6 0 0 :::546 :::* 536/dhcpcd
udp6 0 0 :::5353 :::* 386/avahi-daemon: r
udp6 0 0 :::36316 :::* 386/avahi-daemon: r You can browse the default web content (index.html) that is served by Apache using the curl or wget commands
curl # Command-line tool to transfer data from or to a server using various protocols (HTTP, HTTPS, FTP, etc.)
127.0.0.1 # The IP address of the local machine (localhost), so curl requests the server running on the same device
(RPi) curl 127.0.0.1
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
...
...The index.html location is /var/www/html/index.html, you can change its content using echo or nano commands
sudo # Run the command with superuser (administrator) privileges
/bin/bash # Use the Bash shell to execute the command
-c # Tells Bash to execute the following string as a command
“echo ‘Hello World’” # Prints the text ‘Hello World’
> /var/www/html/index.html # Redirects the output to the file index.html in the web server directory, overwriting it if it exists
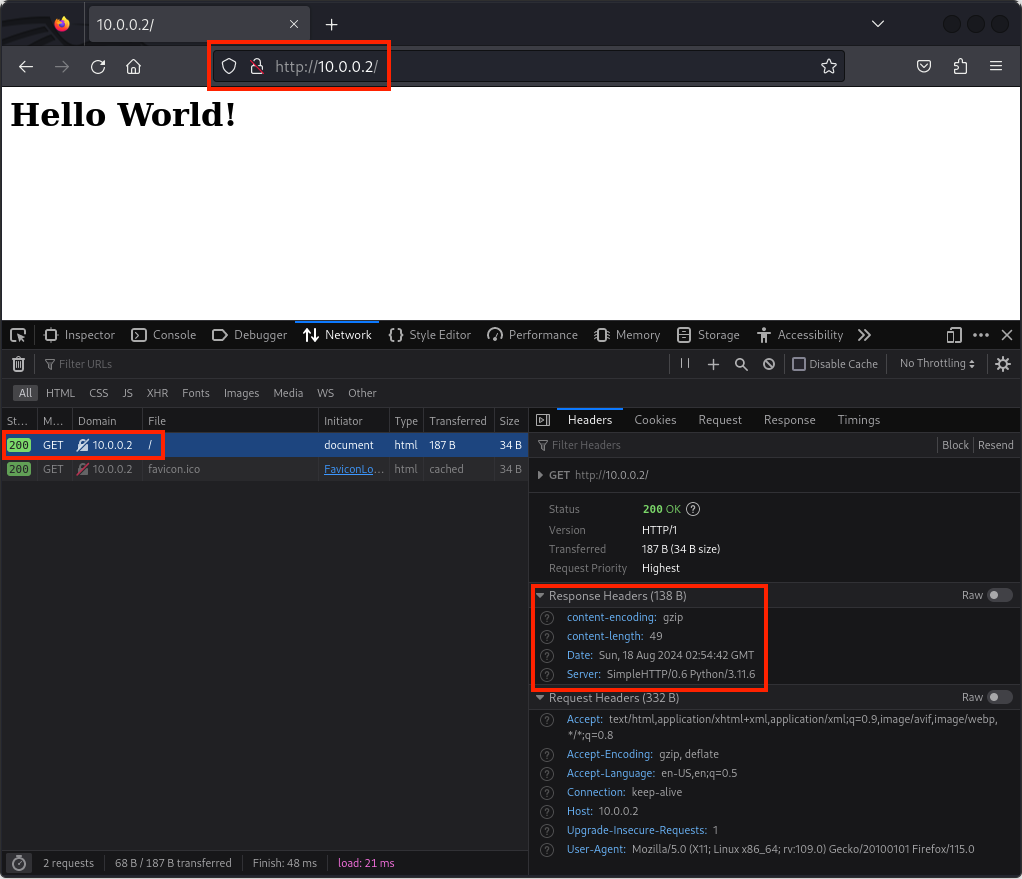
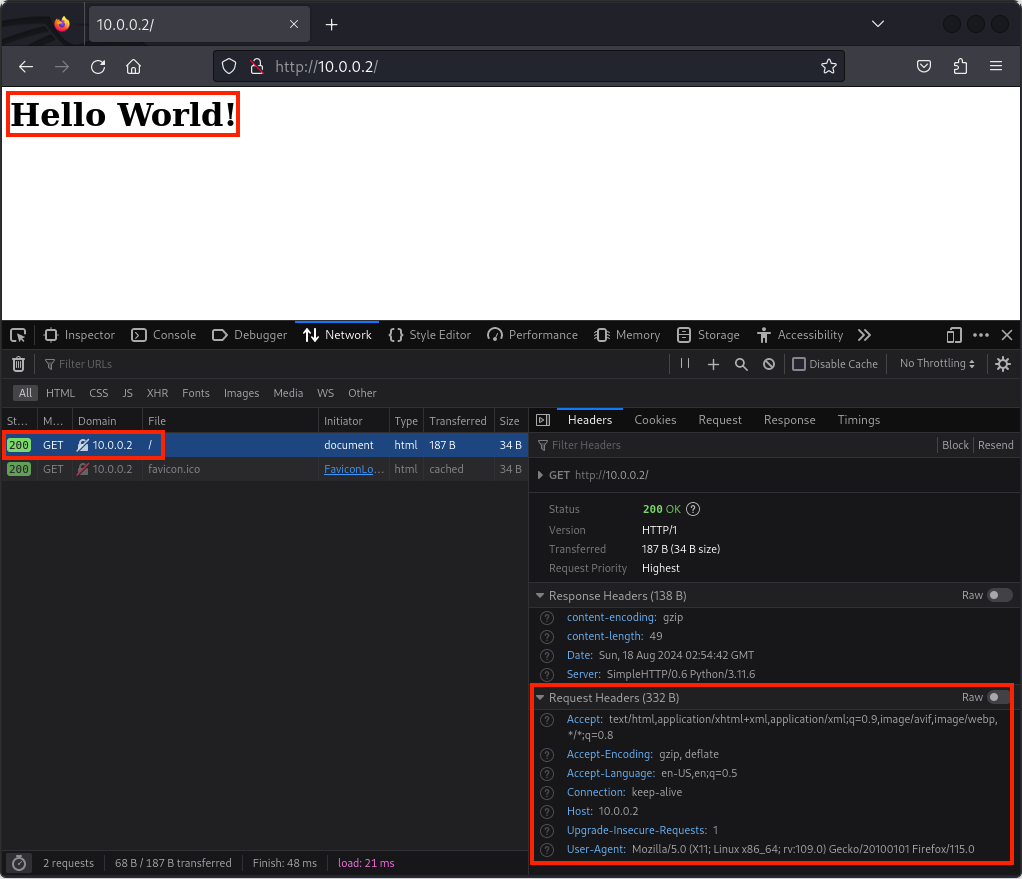
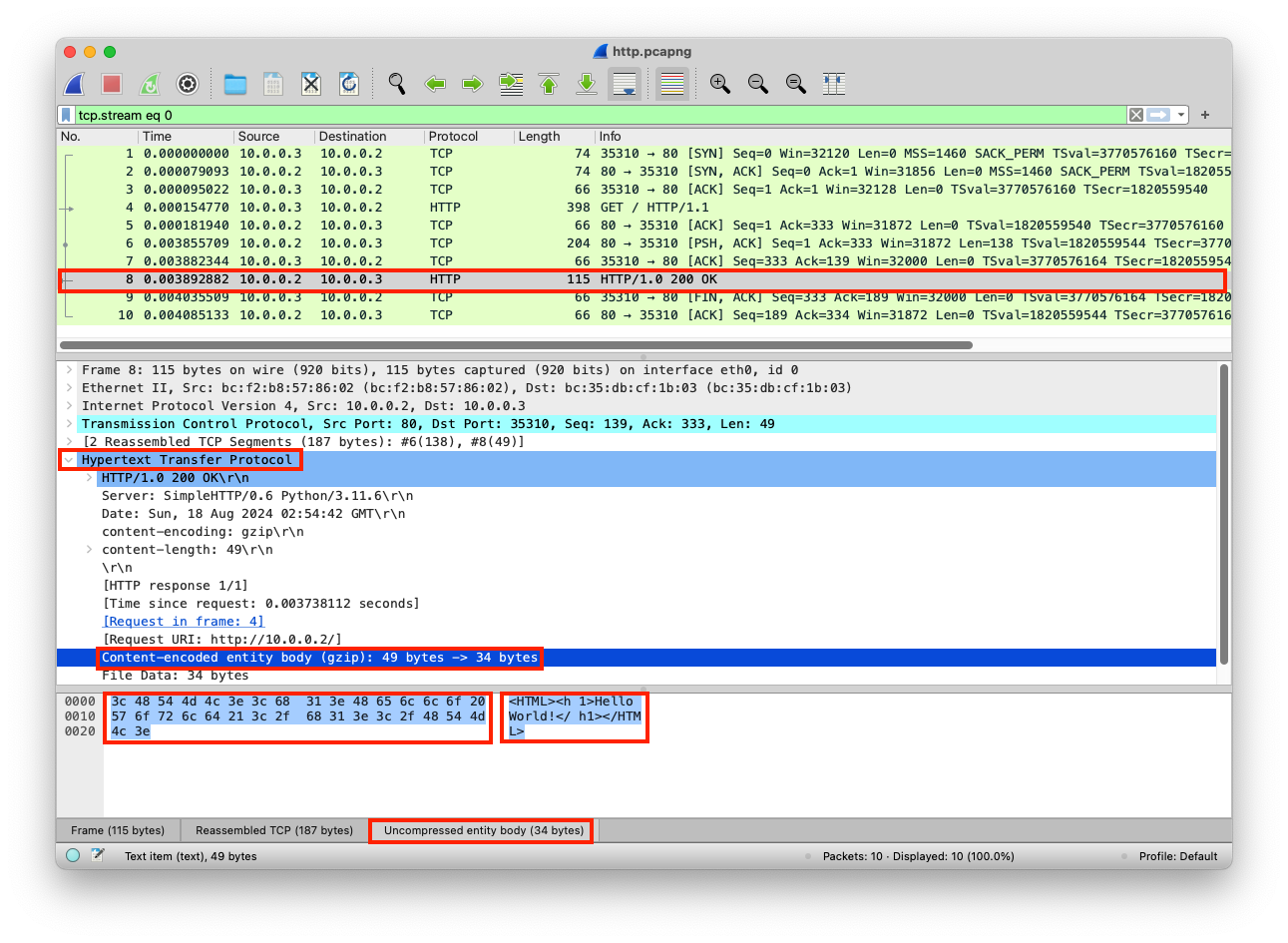
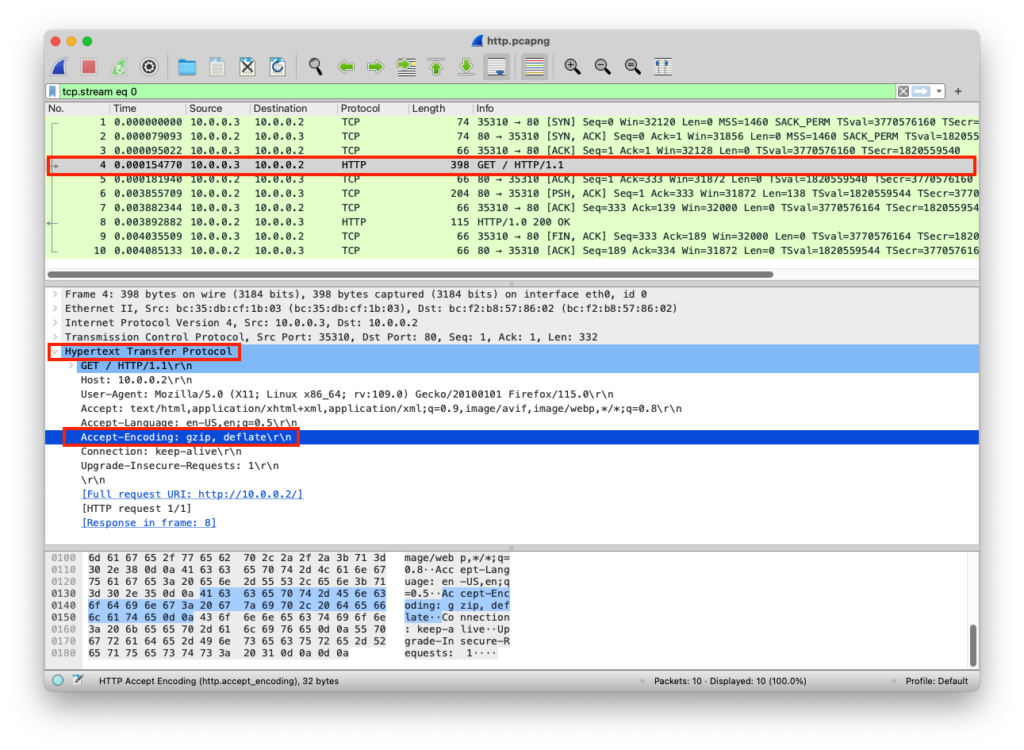
(RPi) sudo /bin/bash -c "echo 'Hello World' > /var/www/html/index.html"When an end-user asks for the web content, they will be getting Hello World
curl # Command-line tool to transfer data from or to a server using various protocols (HTTP, HTTPS, FTP, etc.)
127.0.0.1 # The IP address of the local machine (localhost), so curl requests the server running on the same device
(RPi) curl 127.0.0.1
Hello WorldTo stop the Apache web server, use the systemctl command
sudo # Run the command with superuser privileges
systemctl # Command to control systemd services
stop # Option to stop the specified service immediately
apache2 # The apache2 service to be started
(RPi) sudo systemctl stop apache2You can double-check that by using systemctl status or check if port 80 is still used using the netstat command
sudo # Run the command with superuser privileges
systemctl # Command to control systemd services
status # Option to show the current status of the specified service
apache2 # The apache2 service to be started
(RPi) sudo systemctl status apache2
● apache2.service - The Apache HTTP Server
Loaded: loaded (/lib/systemd/system/apache2.service; enabled; vendor preset: enabled)
Active: inactive (dead) since Sun 2023-08-20 20:38:08 PDT; 1s ago
Docs: https://httpd.apache.org/docs/2.4/
Process: 7251 ExecStop=/usr/sbin/apachectl graceful-stop (code=exited, status=0/SUCCESS)
Main PID: 6883 (code=exited, status=0/SUCCESS)
CPU: 191msOr, netstat (Notice that nothing is listening on port 80)
sudo # Run the following command with superuser (root) privileges
netstat # Network statistics tool that shows network connections, routing tables, interface stats, etc.
-t # Show TCP connections only
-u # Show UDP connections only
-p # Show the PID and name of the program using each socket
-l # Show only listening sockets (services waiting for connections)
-a # Show all sockets (both listening and non-listening)
-n # Show numerical addresses instead of resolving hostnames
(RPi) sudo netstat -tuplan
Active Internet connections (servers and established)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 548/sshd: /usr/sbin
tcp6 0 0 :::22 :::* LISTEN 548/sshd: /usr/sbin
udp 0 0 0.0.0.0:68 0.0.0.0:* 536/dhcpcd
udp 0 0 0.0.0.0:5353 0.0.0.0:* 386/avahi-daemon: r
udp 0 0 0.0.0.0:42997 0.0.0.0:* 386/avahi-daemon: r
udp6 0 0 :::546 :::* 536/dhcpcd
udp6 0 0 :::5353 :::* 386/avahi-daemon: r
udp6 0 0 :::36316 :::* 386/avahi-daemon: r Netcat Webserver
You can create a simple web server using netcat that listens for incoming connections and servers them HTTP header and content, the header HTTP/1.1 200 OK indicates a successful response, and <h1>Hello World</h1> is the content.
sudo # Run the command with superuser (administrator) privileges
apt-get # Linux package management command used to handle software packages
update # Option to refresh the local package index with the latest versions available from repositories
(RPi) sudo apt-get updatesudo # Run the command with superuser (administrator) privileges
apt-get # Linux package management command used to handle software packages
install # Option to install a specified package
netcat # Specify that you want to install the netcat package
(RPi) sudo apt-get install netcatcat # Display file content; here used to create a new file
> script.sh # Redirect the input into a file named script.sh, creating it if it doesn’t exist or overwriting if it does
<<EOF # Start a “here document” (heredoc) that allows you to type multiple lines into the file until the EOF marker is reached
while true; # Infinite loop: keeps running the following commands repeatedly
do
echo -e # Print the string with interpretation of backslash escapes
“http/1.1 200 OK\n\n<h1>Hello World</h1>” # This is an HTTP response with status line 200 OK and a simple HTML body
| # sends that text directly to nc (netcat), which then sends it over the network to any client
nc (netcat) # Command-line utility for network connections
-l # Listen mode (server)
-k # Keep listening after client disconnects
-p 8080 # Listen on port 8080
-q 1 # Quit 1 second after EOF on stdin (optional cleanup)
done
EOF # End of the heredoc; closes file input
(RPi) cat > script.sh <<EOF
while true;
do echo -e "http/1.1 200 OK\n\n<h1>Hello World</h1>" | nc -l -k -p 8080 -q 1;
done
EOFchmod # Change file permissions on a Linux/Unix file
+x # Add execute permission, allowing the file to be run as a program or script
script.sh # The filename to which the permission change is applied
(RPi) chmod +x script.sh./ # Run a program or script located in the current directory
script.sh # The executable script file to run
(RPi) ./script.sh